Is control a form of violence?
How technology supports control
Electronic devises have become an instrument of control. They allow us to know at all times where our partners are, what they are doing and who they are talking to, etc. This can be the prelude to a violent relationship or a relationship of domination.
Social networks as an element of coercion also allow us to virtually harass someone without restrictions of time or space.
The impact of communication technology is not limited to the virtual world. It is important to know that many people have been devastated by them. The danger of becoming a victim of online violence is very real.
Electronic devises have gained importance as instruments of criminal behavior that we have normalized in the name of romantic love. In its name we have learned to justify and accept control, jealousy and so many other unjustifiable behaviors as ‘normal’, because “everybody does it”.
There is also an enormous circulation of ideals and messages, that reproduce traditional gender stereotypes, sexist positions and that promote the use of bodies and specifically women’s bodies as sexual objects.
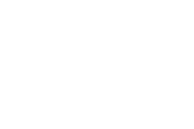
Here are pictures of different phone screens/ screenshots showing examples of controlling behaviours.
Constant messaging

APPROVAL TO SHARE
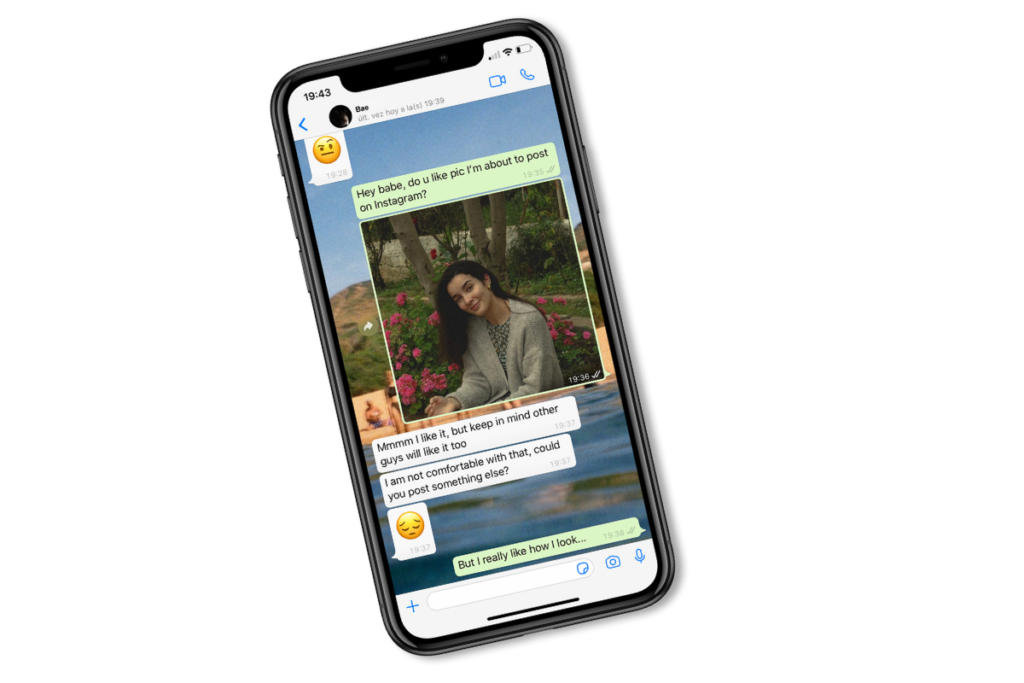
Tracking
Passwords

How is cyber violence used in relationships?
● Hacking: the use of technology to gain illegal or unauthorized access to others online accounts in order to exploit them.
Example: someone hacking into your online account (social media account, bank account, etc.) in order to access and obtain personal information and data to harm you.
● Impersonation: the use of technology to assume the identity of the victim or someone else in order to access private information, embarrass or shame another.
Example: to make an Instagram account with someone’s identity and posting in his/her name.
● Recruitment: use of technology to lure potential victims into violent, abusive and dangerous situations. Example: to message someone to meet with him/her somewhere where the abuse then will happen.
● Revenge porn: someone posting either intimate photographs or videos of another online without their consent, with the aim to publicly shame and humiliate that person. Example: to ask for naked photos from someone privately and afterwards share them publicly on online platforms.